Living in digital age where most of our lives depends to much on cyberworld from business to social medias, threat and risk on the information will always be present. This threat can be as data breach to which threat actors started targeting organizations across industries to either steal data for profit or leak.
With so many breaches occur on previous year, and the documented increase in such attacks a few years prior, one would wonder: How can us – people keep track of whether or not they’ve been affected by these breaches? Do we even realize we’ve been hacked?
What is Have I Been Pwnd ?
Troy Hunt, an Australian cybersecurity expert, blogger, and speaker, created Have I Been Pwned (HIBP), a website that allows internet users to check whether their personal data has been compromised or is part of a trove of leaked data following company breaches, based on the prevalence of data breaches and his analysis of the Adobe attack.
Is it safe and Legit?
Yes, it is correct. HIBP has been around for almost a decade (since 2013) , and it has only proven to be an indispensable tool for common internet users, governments, and organizations alike over that time.
The website does not expressly log anything. Google Analytics, Application Insights performance monitoring, and any diagnostic data unintentionally captured if a system issue occurs are the only sources of logging. It is stated on HIBP FAQ Page.
How to Use Have I Been Pwnd?
- To know and to check if your email address you’re using has been compromised in a data breach, kindly refer to https://haveibeenpwned.com/.
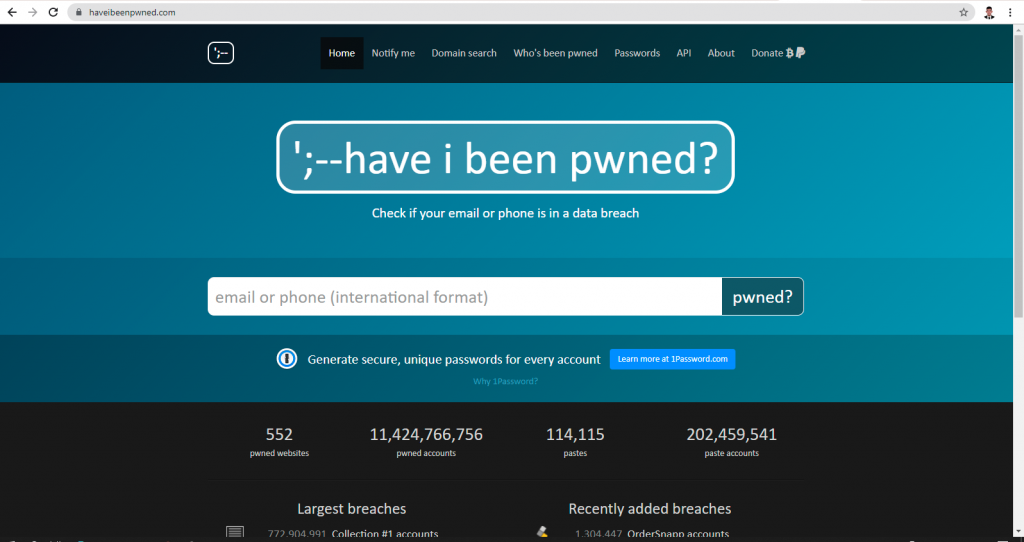
2. Enter your email address on the box and click pwned?. This will search the database to see if your email address is in it and if have been compromised.
3. For the results, if your email address was not involved in a data breach, then you will see a green screen that says, “Good news – no pwnage found!” . If you were compromised by a data breach, you should change your password for the sites where you were allegedly breached, as well as any other sites where you used it if your password was also exposed.
References:
https://blog.malwarebytes.com/awareness/2021/05/have-i-been-pwnd-what-is-it-and-what-to-do-when-you-are-pwned/